Little Brother Competition Answers
Note: it’s quite long (just around 1500 word).
1. Q) Send an encrypted e-mail to one of my two Park Lane e-mail accounts.
A) This e-mail should be encrypted. [It was – ed.]
2. Q) Describe, as well as you can, how you found out how to do it.
A) The steps that I took: (note it was not as straight forward as the following describes – I did many more test emails, little bit of poking around other key servers, etc.)
– Visited https://bookpusheroflessertown.wordpress.com and read everything about this competition.
– I took photos of the clues that were displayed around the school and, when I arrived home, analyzed them, taking notes about things that may seem important (any websites or names).
– I then did some research about the names that I had noted (OpenPGP) and after that, visited the websites from the clues (http://biglumber.com and https://gpgtools.org). I discovered http://biglumber.com is what is called a “key server” (it serves as website where people can upload and find other people’s public keys).
– After getting a larger idea of what everything is, I downloaded the GPG Suite from https://gpgtools.org and installed it onto my Mac.
– When I finished doing more research about encrypting and the GPG Suite, I opened the GPG Keychain application – that came with the GPG Suite – and pressed “New”. I filled in all my details (name, e-mail address) and unchecking the “Key Expires” box, then generated my key.
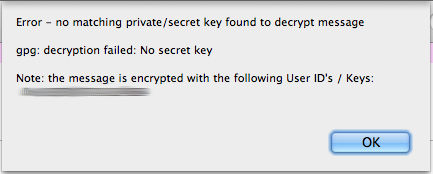
– After doing more research on the process of encrypting and decrypting an email, I ran a couple tests, sending the encrypted e-mail to a second account and decrypting it, finding that everything was in order.
– Taking a look at how to encrypt an e-mail with a public key, I went to the key server, http://biglumber.com, and went around, digging for any reference to the library e-mail address.
– After some looking around for a bit, I found the library’s public key in View listings > Prague, Czech Republic and clicking on the fingerprint.
– Following that, I copied it into a TextEdit document and named the document using example provided by the key server in which that public key is stored (pubkey.78126D0601E3631.Librarian.asc).
– I then imported the public key into my keychain by dragging it in.
– When I inspected everything to make sure everything was good, I opened up the mail application and wrote my test e-mail that I would send you. When I finished filling in your e-mail address and typing the short length of text and I pressed the small lock icon (which encrypts the e-mail), I sent it.
– After I received the e-mail from you telling me the encryption was correct, I wrote this e-mail and I will sent it in the same fashion.
3. Q) Describe, as well as you can, why anybody would need or desire to do it.
A) People would want to encrypt an e-mail to prevent any prying eyes to see the e-mail’s contents. Normally someone would encrypt an e-mail containing information only they and the person they are sending the encrypted e-mail to would want to read (e.g.: account information, sporting match strategies and other private matters).
4. Q) Describe, as clearly as you can, how someone can do the same.
A) Step-by-step instructions:
Stuff you need:
– A Mac (I do not know how to do it on a Windows/Linux)
– Your administrator password
– The public key of the person who you want to send the encrypted e-mail to
Method:
1. Open you Mac and go to https://gpgtools.org. Scroll down a little and click “Download GPG Suite” (note: NOT “GPG Suite Beta 4”).
2. After it downloaded, open it and install. You will need the administrator’s password in order to install it correctly.
3. After that, go to the search bar (or Command+Space Bar) and type in “GPG Keychain”. Once you have found it, open it.
4. You are going to want to create your own key, so click “New” in the top left-hand corner.
5. Then, fill in your full name and e-mail address. Check the “Upload public key after generation” box as well. Drop down the advanced options and decide if you want your key to expire (uncheck the box if you don’t want it to and check it if you do – but if you do this then you will have to change the expiry date to whatever you see fit). Once you are done, click “Generate key”. You will be asked to create a passphrase so do it – make sure you keep you passphrase a secret!
6. After that, find public key belonging to the person you want to send the encrypted e-mail to. Tell him/her to either tell you which key server it is on or him/her to send it to you.
7. Once you have acquired the public key, make sure the extension is .asc but if not then change it to that.
8. When you made sure its .asc (the icon should look like a document with keys on it with ASC underneath), drag your friend’s public key into the GPG Keychain. This imports the public key to your keychain.
9. After you have done that, open the Mail application (that comes pre-installed when you first buy your Mac). I suggest you use the Mail application because it is easier.
10. Compose a new letter (there should be 3 differences: a greyed-out tab in the top right-hand corner and two buttons next to the “From:” section: one a lock to encrypt the e-mail, the other to sign it) and fill the “To:” section with your friend’s e-mail address like you would do normally. Make sure your e-mail address is the one you inputted when you created your key. Write the email.
11. When the e-mail has been written and all the information is correct, the greyed out “OpenPGP” tab will become green. When that happens, click the lock button so that the lock is closed. This means that the e-mail will be encrypted.
12. Once you have done that, click send!
13. If you receive a reply that is encrypted, copy and paste the entire response into a text document of your choice.
14. Then, select the entirety of the encrypted response and go to the top with your text document’s name and go to “Services”. Once you have found that, find the “OpenPGP: Decrypt Selection” and click it. Enter the passphrase of you private key and it should convert from the gibberish that was before to legible text.
5. Q) Describe, as well as you can, anything you learned in the course of researching for this competition that you were not directly looking for.
A) I always hear people say that they are so vulnerable to hackers and spies and they can do nothing about it, but, combined with a bit of effort, you can be more secure on a computer than you might think. Also that being secure is a hard thing to get a grip of but once you do understand and get a good idea of what you are doing, it seems… natural and not as arduous as other people may think. So yes, I did learn a bunch of things about morality and understanding the Internet.
6. Q) If competing as a group, describe, as well as you can, what roles you took and how you worked together, as well as any problems you had.
A) I was working solo so all the roles were played by me. I encountered many problems along the course of this competition though. First off, my most major issue and took the longest to solve was encrypting an e-mail with the library’s public key. The fact that GPG Keychain constantly could not find the library public key on the key server bugged me and after a long and strenuous think spanning a couple of days, I decided to keep it simple and not overcomplicate it by just not finding the key on the key server and hope GPG Keychain would automatically find and select the public key when I inputted the library e-mail address into to “To:” section. And surprise, surprise, it worked. I should also add to the answer of question #5 that you should never underestimate what sophisticated software can do.
A few minor problems showed up along the way, for example me not being able to find the library’s public key, but that was solved swiftly when I double-checked the websites and eventually uncovered it in http://biglumber.com.
7. Q) Describe, as well as you can, what you most enjoyed about this competition.
A) I enjoyed, as I am sure other would enjoy, the feeling of when you find something you have been looking for is quite thrilling, especially if it is a major part to the project, for example finding the library’s public key and when I realized my encrypting is correct. As well as that, I enjoyed the overall experience, researching as seeing what wonders are hidden in the world of computers.